Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
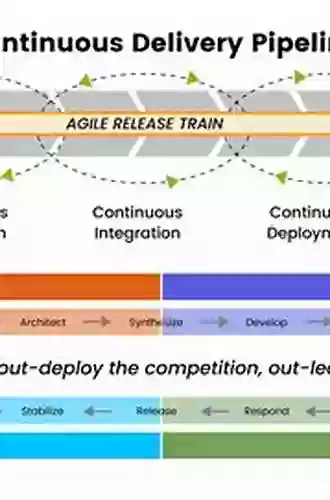
Boosting Your Continuous Delivery Pipeline: Implementing Effective Security Measures

Welcome to the era of continuous delivery! Organizations worldwide are increasingly adopting agile practices and DevOps methodologies to ensure the rapid and efficient delivery of software applications. As development cycles continue to shrink, the need for a seamless and secure continuous delivery pipeline becomes paramount.
In this article, we will explore the importance of enabling security in the continuous delivery pipeline and discuss actionable steps to integrate effective security measures into your development process. By implementing these measures, you can significantly reduce the risk of security breaches and safeguard your applications and sensitive data.
Why Security Should be a Crucial Component of Your Continuous Delivery Pipeline
Traditionally, security has been an afterthought in software development processes. Developers focused primarily on functionality and speed, often overlooking security concerns until late in the development lifecycle. However, this approach is no longer sustainable in today's rapidly evolving threat landscape.
4.4 out of 5
| Language | : | English |
| File size | : | 2337 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 554 pages |
| Screen Reader | : | Supported |
By considering security from the start of your continuous delivery pipeline, you can effectively address vulnerabilities and mitigate risk, protecting your applications and infrastructure from potential attacks. Integrating security into the development process also ensures that your applications adhere to regulatory compliance standards, enhancing customer trust and reducing legal and financial risks.
The Continuous Delivery Pipeline: Key Stages
Before we delve into the security measures, let's briefly understand the key stages of a continuous delivery pipeline:
- Code: Developers create and test code changes locally, ensuring the implementation of secure coding practices.
- Build: Code changes are built into deployable artifacts, including binaries and necessary configurations.
- Test: Automated tests are executed to validate the functionalities and identify any potential issues.
- Release: Approved changes are deployed to a production-like environment, and further tests are conducted.
- Deploy: Changes that pass all tests are deployed to production, making the software available to end-users.
- Operate: Continuous monitoring and feedback loops ensure that the software performs as intended and any issues are quickly identified and resolved.
Integrating Effective Security Measures
1. Secure Code Practices and Review
Implementing secure coding practices from the start is crucial. Train your developers on secure coding techniques and conduct regular code reviews to identify potential vulnerabilities. Tools like static code analysis can also assist in identifying security flaws early in the development process.
Consider using vulnerability scanners or manual penetration testing to identify any weaknesses in your application. Continuous monitoring and updating of dependencies can help address any security vulnerabilities that arise.
2. Automated Security Testing
Automated security testing should be an integral part of your continuous delivery pipeline. Tools like dynamic application security testing (DAST) and static application security testing (SAST) can identify runtime vulnerabilities and code-level flaws, respectively.
Integrate security testing into your build and release processes, ensuring that vulnerabilities are identified and addressed before changes are deployed. Implementing infrastructure-as-code and regularly scanning your infrastructure for misconfigurations can also minimize security risks.
3. API Security
Secure APIs are vital for protecting sensitive data and ensuring smooth communication between applications. Implement measures such as authentication, access controls, and encryption to safeguard your APIs from unauthorized access and malicious attacks.
Regularly perform security assessments on your APIs to identify vulnerabilities and address them promptly. Adopting standards like OAuth and OpenID Connect can enhance the security of your API endpoints.
4. Container Security
If you are leveraging containers in your continuous delivery pipeline, ensuring their security is crucial. Container orchestration platforms like Kubernetes provide numerous security features, but they require proper configuration and ongoing monitoring.
Regularly scan your container images for vulnerabilities and weaknesses. Monitor your containers' runtime behavior and use role-based access controls (RBAC) to restrict unnecessary privileges. Additionally, keep your container runtime and orchestrator up to date with the latest security patches.
5. Secure Deployment and Configuration Management
Adopt secure deployment practices and maintain strict control over your configuration management process. Implement robust access controls, least privilege principles, and secure communication channels between your different deployment environments.
Automate your deployment process while ensuring strict validation of deployment artifacts to minimize the risk of unauthorized changes. Utilize secrets management solutions to securely store and access sensitive configuration data.
6. Continuous Monitoring and Incident Response
Implement a comprehensive monitoring and incident response system to detect and respond to security incidents quickly. Leverage tools that provide real-time visibility into your applications and infrastructure.
Set up automated logging, monitoring, and alerting mechanisms to actively track any suspicious activities. Define incident response protocols in advance and conduct regular drills to ensure your team is well-prepared to handle security incidents effectively.
As organizations strive for rapid and reliable software delivery through their continuous delivery pipelines, security should be a fundamental element throughout the entire development process. By implementing the security measures discussed in this article, you can significantly enhance the security posture of your software applications and protect against potentially devastating attacks.
Remember, enabling security in your continuous delivery pipeline is not a one-time task; it requires ongoing commitment, automation, and continuous improvement. Embrace security as an integral part of your development and deployment processes, and stay one step ahead of potential threats.
So, start today and secure your continuous delivery pipeline to build resilient software and gain the trust of your customers!
4.4 out of 5
| Language | : | English |
| File size | : | 2337 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 554 pages |
| Screen Reader | : | Supported |
Agile continues to be the most adopted software development methodology among organizations worldwide, but it generally hasn't integrated well with traditional security management techniques. And most security professionals aren’t up to speed in their understanding and experience of agile development. To help bridge the divide between these two worlds, this practical guide introduces several security tools and techniques adapted specifically to integrate with agile development.
Written by security experts and agile veterans, this book begins by introducing security principles to agile practitioners, and agile principles to security practitioners. The authors also reveal problems they encountered in their own experiences with agile security, and how they worked to solve them.
You’ll learn how to:
- Add security practices to each stage of your existing development lifecycle
- Integrate security with planning, requirements, design, and at the code level
- Include security testing as part of your team’s effort to deliver working software in each release
- Implement regulatory compliance in an agile or DevOps environment
- Build an effective security program through a culture of empathy, openness, transparency, and collaboration

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Arthur C. ClarkeSouvenir Of The 8th Army Corps Philippine Expedition: Discover the Untold...
Arthur C. ClarkeSouvenir Of The 8th Army Corps Philippine Expedition: Discover the Untold...
 Clarence MitchellKorea's Remarkable Development Under Park Chung Hee: A Testament to Routledge...
Clarence MitchellKorea's Remarkable Development Under Park Chung Hee: A Testament to Routledge...
 Hector BlairDiscover the Delightful World of Poppy Seed Recipes: 150 Mouthwatering Ideas!
Hector BlairDiscover the Delightful World of Poppy Seed Recipes: 150 Mouthwatering Ideas! Easton PowellFollow ·7.2k
Easton PowellFollow ·7.2k Charles BukowskiFollow ·16.2k
Charles BukowskiFollow ·16.2k Devin RossFollow ·8.9k
Devin RossFollow ·8.9k Elton HayesFollow ·11.4k
Elton HayesFollow ·11.4k Kyle PowellFollow ·3.2k
Kyle PowellFollow ·3.2k Eugene PowellFollow ·7.1k
Eugene PowellFollow ·7.1k Willie BlairFollow ·9.8k
Willie BlairFollow ·9.8k Jorge AmadoFollow ·4.8k
Jorge AmadoFollow ·4.8k