Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
The Art of Cryptography: TLS and its Attack-Resistant Features

to Cryptography
Cryptography has become an integral part of our digital lives. Whether we're making online transactions, sending sensitive information, or even just browsing the web, cryptography protects our data from prying eyes. In this article, we will dive deep into the world of cryptography, focusing on Transport Layer Security (TLS) and its attack-resistant features.
What is Transport Layer Security (TLS)?
Transport Layer Security, commonly known as TLS, is a cryptographic protocol that ensures secure communication over computer networks. It is the successor to Secure Sockets Layer (SSL) and has become the industry standard for establishing encrypted connections between web servers and clients. TLS is primarily used to secure web traffic, including emails, instant messaging, and online transactions.
The Working of TLS
TLS employs a combination of symmetric and asymmetric encryption algorithms to establish a secure connection between two parties. It begins with a handshake protocol, where the client and server authenticate each other and negotiate the encryption algorithms and keys to be used. This ensures that the messages exchanged between them are encrypted and cannot be intercepted or tampered with by malicious entities.
4.5 out of 5
| Language | : | English |
| File size | : | 6827 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 502 pages |
Attack Resistance in TLS
While TLS provides a robust encryption mechanism, it's not immune to attacks. However, it incorporates various features to resist and mitigate potential attacks. Let's explore some of these attack-resistant features:
1. Certificate Validation
TLS relies on digital certificates issued by trusted Certificate Authorities (CAs) to verify the authenticity of servers. Certificate validation ensures that the server's identity matches the one listed in its certificate. This prevents attackers from impersonating legitimate servers and intercepting sensitive data.
2. Perfect Forward Secrecy (PFS)
PFS is a critical feature of TLS that ensures the secrecy of past sessions even if a private key is compromised in the future. It achieves this by generating a unique session key for each session, making it impossible to decrypt previous sessions' data if the private key is compromised later.
3. Cipher Suite Selection
TLS supports various cipher suites, each using different encryption algorithms and key exchange methods. The client and server negotiate and select an appropriate cipher suite based on their supported capabilities. This helps ensure the strongest encryption possible while considering the performance requirements and compatibility of both parties.
4. Renegotiation Protection
TLS includes mechanisms to protect against potential renegotiation attacks. Renegotiation allows parties to modify parameters after the initial handshake. However, if not properly secured, it can be exploited by attackers. TLS employs secure renegotiation techniques to prevent such attacks.
5. Resistance against Eavesdropping and Tampering
TLS uses encryption algorithms to protect data in transit from eavesdropping and tampering attempts. By encrypting the communications between the client and server, TLS ensures that even if the data is intercepted, it remains confidential and cannot be understood or modified.
Future Challenges in TLS
As with any technology, the ever-evolving threat landscape presents challenges for TLS. Some of these challenges include the rise of quantum computers that may potentially break current encryption algorithms, the need for post-quantum cryptography, and the continuous development of new attack techniques. Addressing these challenges is crucial for maintaining the security of TLS in the years to come.
Transport Layer Security (TLS) plays a vital role in securing our online communications and transactions. Its attack-resistant features, such as certificate validation, perfect forward secrecy, and strong encryption algorithms, provide a robust defense against malicious entities. As the digital landscape evolves, it is imperative to stay updated with the latest advancements and challenges in cryptography to ensure the continued security of our data.
4.5 out of 5
| Language | : | English |
| File size | : | 6827 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 502 pages |
Full Stack Python Securityteaches you everything you’ll need to build secure Python web applications.
Summary
In Full Stack Python Security: Cryptography, TLS, and attack resistance, you’ll learn how to:
Use algorithms to encrypt, hash, and digitally sign data
Create and install TLS certificates
Implement authentication, authorization, OAuth 2.0, and form validation in Django
Protect a web application with Content Security Policy
Implement Cross Origin Resource Sharing
Protect against common attacks including clickjacking, denial of service attacks, SQL injection, cross-site scripting, and more
Full Stack Python Security: Cryptography, TLS, and attack resistance teaches you everything you’ll need to build secure Python web applications. As you work through the insightful code snippets and engaging examples, you’ll put security standards, best practices, and more into action. Along the way, you’ll get exposure to important libraries and tools in the Python ecosystem.
Purchase of the print book includes a free eBook in PDF, Kindle, and ePub formats from Manning Publications.
About the technology
Security is a full-stack concern, encompassing user interfaces, APIs, web servers, network infrastructure, and everything in between. Master the powerful libraries, frameworks, and tools in the Python ecosystem and you can protect your systems top to bottom. Packed with realistic examples, lucid illustrations, and working code, this book shows you exactly how to secure Python-based web applications.
About the bookFull Stack Python Security: Cryptography, TLS, and attack resistance teaches you everything you need to secure Python and Django-based web apps. In it, seasoned security pro Dennis Byrne demystifies complex security terms and algorithms. Starting with a clear review of cryptographic foundations, you’ll learn how to implement layers of defense, secure user authentication and third-party access, and protect your applications against common hacks.
What's inside
Encrypt, hash, and digitally sign data
Create and install TLS certificates
Implement authentication, authorization, OAuth 2.0, and form validation in Django
Protect against attacks such as clickjacking, cross-site scripting, and SQL injection
About the reader
For intermediate Python programmers.
About the authorDennis Byrne is a tech lead for 23andMe, where he protects the genetic data of more than 10 million customers.
Table of Contents
1 Defense in depth
PART 1 - CRYPTOGRAPHIC FOUNDATIONS
2 Hashing
3 Keyed hashing
4 Symmetric encryption
5 Asymmetric encryption
6 Transport Layer Security
PART 2 - AUTHENTICATION AND AUTHORIZATION
7 HTTP session management
8 User authentication
9 User password management
10 Authorization
11 OAuth 2
PART 3 - ATTACK RESISTANCE
12 Working with the operating system
13 Never trust input
14 Cross-site scripting attacks
15 Content Security Policy
16 Cross-site request forgery
17 Cross-Origin Resource Sharing
18 Clickjacking

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
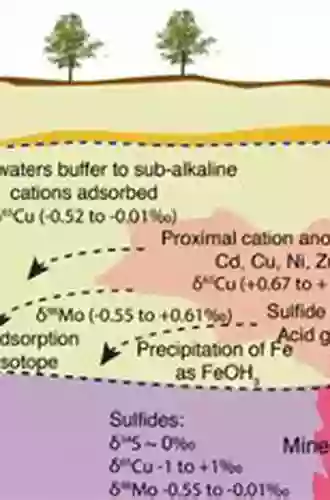
 Lawrence BellUnraveling the Mysteries of Groundwater Geochemistry and Isotopes: A Closer...
Lawrence BellUnraveling the Mysteries of Groundwater Geochemistry and Isotopes: A Closer...
 Brett SimmonsUnlock Your Full Potential: Get Started Editing Files With The Linux Command...
Brett SimmonsUnlock Your Full Potential: Get Started Editing Files With The Linux Command...
 Quentin PowellThe Roman Empire and the Silk Routes: A Tale of Trade, Power, and Cultural...
Quentin PowellThe Roman Empire and the Silk Routes: A Tale of Trade, Power, and Cultural...
 Dwayne MitchellDiscover Harmony and Relaxation: Box Set Chakras and Bath Bombs Chakras Bath...
Dwayne MitchellDiscover Harmony and Relaxation: Box Set Chakras and Bath Bombs Chakras Bath...
 Eugene PowellThe Captivating Storytelling of Circulo Esfera: A Journey Into the World of...
Eugene PowellThe Captivating Storytelling of Circulo Esfera: A Journey Into the World of... Jackson BlairFollow ·12.6k
Jackson BlairFollow ·12.6k John GrishamFollow ·19.8k
John GrishamFollow ·19.8k Melvin BlairFollow ·5.3k
Melvin BlairFollow ·5.3k Zachary CoxFollow ·9.2k
Zachary CoxFollow ·9.2k Juan ButlerFollow ·6.6k
Juan ButlerFollow ·6.6k Scott ParkerFollow ·4.9k
Scott ParkerFollow ·4.9k Wesley ReedFollow ·15.7k
Wesley ReedFollow ·15.7k David Foster WallaceFollow ·16.8k
David Foster WallaceFollow ·16.8k