Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
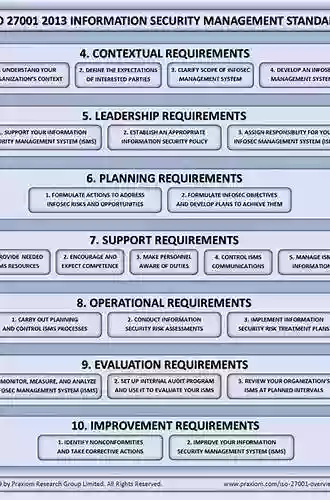
Why You Need to Implement an Information Security Management System (ISMS)

With the ever-increasing threat of cyberattacks, safeguarding your organization's information has become paramount. Implementing an Information Security Management System (ISMS) is a crucial step towards protecting your sensitive data from unauthorized access, disclosure, and modification.
But what exactly is an ISMS, and why is it necessary?
Understanding ISMS
An ISMS is a systematic approach to managing sensitive information within an organization. It encompasses people, processes, and technology to establish a robust framework for managing the organization's information security risks. The primary goal of an ISMS is to maintain the confidentiality, integrity, and availability of valuable information assets.
4.2 out of 5
| Language | : | English |
| File size | : | 11232 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 294 pages |
By implementing an ISMS, organizations can ensure the secure handling of their data, protect their reputation, and meet regulatory and legal requirements. It also helps build customer trust, as clients are more likely to work with businesses that prioritize data security.
The Benefits of Implementing an ISMS
Implementing an ISMS offers numerous benefits to organizations of all sizes, including:
1. Enhanced Information Security
An ISMS provides a comprehensive approach to information security, ensuring that proper controls and safeguards are in place. It allows organizations to identify and address vulnerabilities and implement measures to minimize the risk of information breaches.
2. Regulatory Compliance
Organizations are increasingly subject to legal and industry-specific regulations concerning data security. Implementing an ISMS helps ensure compliance with these regulations, avoiding hefty fines and penalties.
3. Customer Trust and Brand Reputation
Data breaches can severely damage a company's reputation and erode customer trust. By implementing an ISMS, organizations demonstrate their commitment to protecting customer data, strengthening their brand image, and attracting potential clients who value data security.
4. Increased Business Opportunities
Many organizations now require partners and suppliers to showcase their commitment to information security. By implementing an ISMS, you gain a competitive advantage and open doors to new business opportunities.
5. Cost Savings
Investing in an ISMS can save organizations money in the long run. By identifying and remedying security vulnerabilities early on, businesses can minimize the costs associated with data breaches, downtime, and recovery.
Implementing an ISMS in Five Steps
Now that you understand the importance of implementing an ISMS, let's delve into the five essential steps to get you started:
1. Establish the Context
Before implementing an ISMS, you need to understand your organization's risk appetite, business objectives, and legal obligations. This step involves conducting a thorough risk assessment to identify the assets you need to protect, potential threats and vulnerabilities, and the impact of any potential incidents.
2. Develop the Framework
Once you have a clear understanding of your organization's information security risks, it's time to develop a framework that outlines the security controls needed to mitigate those risks. The framework should align with industry standards and best practices, such as the ISO 27001 standard.
3. Implement the Controls
Implementing the security controls outlined in your framework is a critical step in securing your information. This may involve establishing access controls, encryption protocols, employee training programs, and incident response plans.
4. Monitor and Evaluate
An effective ISMS requires continuous monitoring and evaluation. Regularly assess and analyze your organization's security controls, identify any gaps or weaknesses, and take appropriate corrective actions. Implementing a robust security incident response plan is also crucial to ensure quick and effective responses to any breaches.
5. Maintain and Improve
An ISMS is an ongoing process that requires regular maintenance and improvement. Stay updated with the latest threats and technologies, conduct regular audits, provide training to employees, and review and update your security controls as needed.
The implementation of an Information Security Management System is no longer an option but a necessity in today's digital landscape. With cyber threats becoming more sophisticated and prevalent, organizations need to prioritize the protection of their information assets.
By implementing an ISMS, you enhance information security, ensure compliance with regulations, build trust with customers, unlock new business opportunities, and save costs in the long run.
Secure your organization's data by implementing an ISMS today and stay one step ahead in the fight against cybercrime.
4.2 out of 5
| Language | : | English |
| File size | : | 11232 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 294 pages |
Discover the simple steps to implementing information security standards using ISO 27001, the most popular information security standard across the world. You’ll see how it offers best practices to be followed, including the roles of all the stakeholders at the time of security framework implementation, post-implementation, and during monitoring of the implemented controls. Implementing an Information Security Management System provides implementation guidelines for ISO 27001:2013 to protect your information assets and ensure a safer enterprise environment.
This book is a step-by-step guide on implementing secure ISMS for your organization. It will change the way you interpret and implement information security in your work area or organization.
What You Will Learn
- Discover information safeguard methods
- Implement end-to-end information security
- Manage risk associated with information security
- Prepare for audit with associated roles and responsibilities
- Identify your information risk
- Protect your information assets
Who This Book Is For
Security professionals who implement and manage a security framework or security controls within their organization. This book can also be used by developers with a basic knowledge of security concepts to gain a strong understanding of security standards for an enterprise.

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Clarence BrooksClimate Adaptation Finance And Investment In California: A Key Solution for a...
Clarence BrooksClimate Adaptation Finance And Investment In California: A Key Solution for a...
 Jamie BlairOne Way Translation Tool For Collins School Dictionaries - Unlock the World...
Jamie BlairOne Way Translation Tool For Collins School Dictionaries - Unlock the World... Chris ColemanFollow ·8.4k
Chris ColemanFollow ·8.4k Reed MitchellFollow ·4.9k
Reed MitchellFollow ·4.9k Kendall WardFollow ·5.2k
Kendall WardFollow ·5.2k Heath PowellFollow ·17.7k
Heath PowellFollow ·17.7k Eugene PowellFollow ·7.1k
Eugene PowellFollow ·7.1k Harrison BlairFollow ·10.7k
Harrison BlairFollow ·10.7k Wayne CarterFollow ·11.6k
Wayne CarterFollow ·11.6k Herbert CoxFollow ·9.8k
Herbert CoxFollow ·9.8k