Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
Unlocking the Secrets of Malware Forensics: Your Ultimate Field Guide for Linux Systems

The World of Malware Forensics on Linux
In the digital age, cybercrime has become an ever-increasing threat, affecting individuals, organizations, and governments alike. Protecting our digital assets from malicious attacks has become imperative, and understanding how to investigate and mitigate the aftermath of malware incidents is crucial. This comprehensive field guide explores the realm of malware forensics specifically tailored for Linux systems, equipping you with the necessary knowledge and tools to combat these threats effectively.
Understanding Malware Forensics
Before delving into the intricacies of malware forensics on Linux systems, it is essential to grasp the fundamental concepts of this field. Malware forensics is the science of examining and analyzing digital evidence left by malicious software. It involves investigating the behavior, impact, and origin of malware attacks to identify the attacker and gather evidence for future legal actions. This first section will provide you with a comprehensive overview of the principles and methodologies of malware forensics, enabling you to approach Linux-based investigations confidently.
4.7 out of 5
| Language | : | English |
| File size | : | 16579 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 864 pages |
Navigating a Linux-Based Malware Investigation
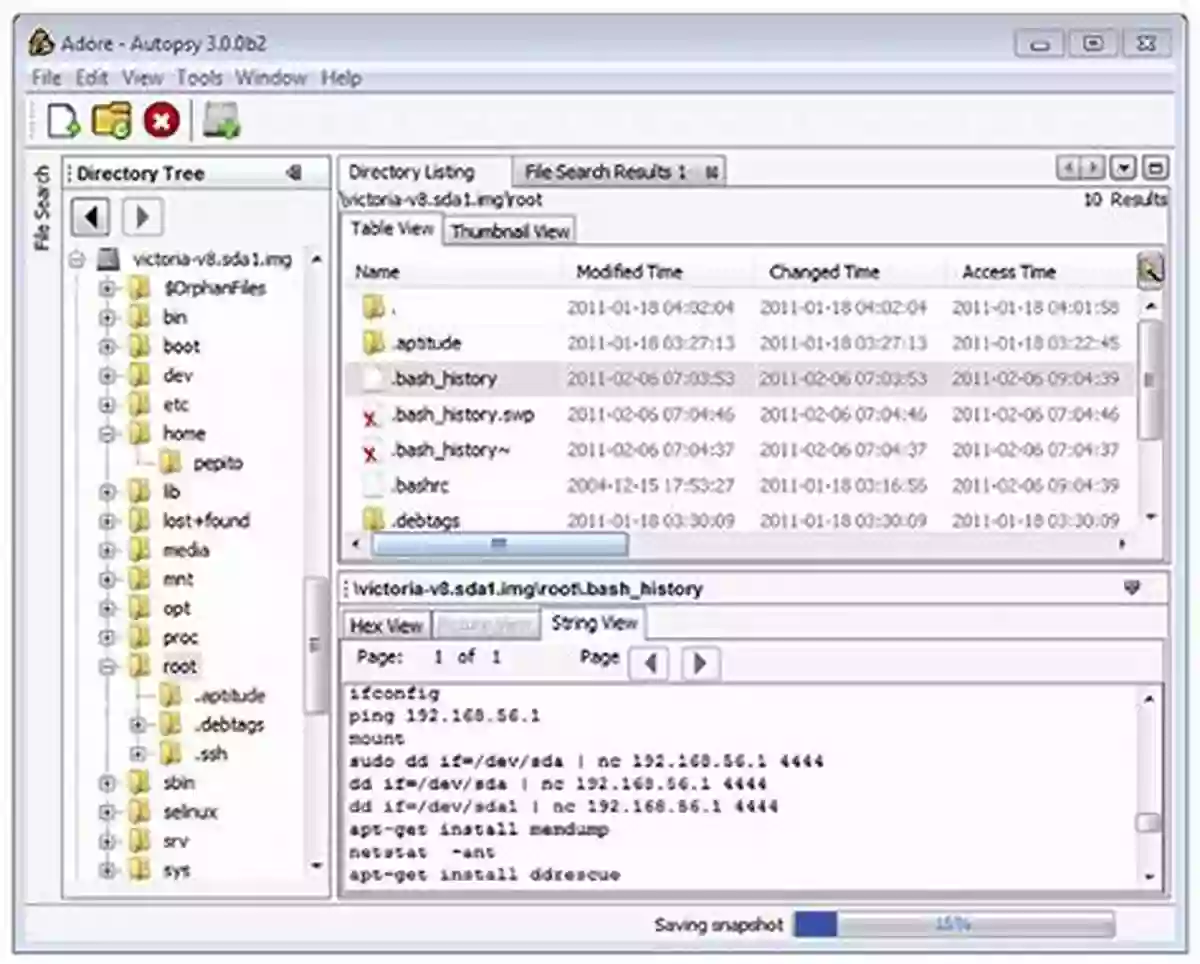
Linux is known for its robust security features, but it is not immune to malware attacks. When dealing with a suspected malware incident on a Linux system, forensic analysts must possess a deep understanding of its file system, processes, and network architecture. This section will unveil the inner workings of Linux systems, equip you with the necessary tools and techniques to identify and analyze malware, and provide step-by-step guidelines for conducting a Linux-based malware investigation. By the end of this section, you will be well-prepared to tackle any malicious attack and unearth valuable evidence on Linux-based devices.
Unmasking Advanced Linux Malware Techniques
As cybercriminals continuously evolve their tactics, traditional methods of malware analysis may no longer suffice. This section will dive into the realm of advanced Linux malware techniques, such as rootkits, bootkits, and kernel-level attacks. We will explore the tools and methodologies required to identify and analyze these covert forms of malware, empowerning you to detect and mitigate even the most sophisticated Linux threats. Prepare to uncover the hidden depths of Linux malware and level up your forensics skills to the next level.
Best Practices and Industry Insights
In the ever-evolving world of cybersecurity, staying up-to-date with the latest industry practices and insights is crucial. This section will guide you through the best practices employed by professionals in the field of malware forensics, including network security, incident response, and forensic toolkits for Linux systems. Additionally, we will shed light on real-life case studies, examining notable incidents and showcasing the techniques utilized to investigate and solve them. Whether you are an aspiring professional or a seasoned expert, this section will provide you with invaluable knowledge that will keep you at the forefront of the industry.
A Resilient Defense Against Linux Malware
In an age where cyber threats are rampant, arming ourselves with the essential knowledge and tools to combat and investigate malware attacks is paramount. This malware forensics field guide for Linux systems serves as your ultimate companion in unraveling the nuances of this specialized field. Through a comprehensive exploration of the principles, methodologies, and best practices, you will emerge prepared to tackle even the most sophisticated Linux-based malware attacks. Stay ahead of the game by mastering the secrets of malware forensics for Linux systems and become an invaluable asset in the fight against cybercrime.
4.7 out of 5
| Language | : | English |
| File size | : | 16579 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 864 pages |
Malware Forensics Field Guide for Linux Systems is a handy reference that shows students the essential tools needed to do computer forensics analysis at the crime scene. It is part of Syngress Digital Forensics Field Guides, a series of companions for any digital and computer forensic student, investigator or analyst. Each Guide is a toolkit, with checklists for specific tasks, case studies of difficult situations, and expert analyst tips that will aid in recovering data from digital media that will be used in criminal prosecution.
This book collects data from all methods of electronic data storage and transfer devices, including computers, laptops, PDAs and the images, spreadsheets and other types of files stored on these devices. It is specific for Linux-based systems, where new malware is developed every day. The authors are world-renowned leaders in investigating and analyzing malicious code. Chapters cover malware incident response - volatile data collection and examination on a live Linux system; analysis of physical and process memory dumps for malware artifacts; post-mortem forensics - discovering and extracting malware and associated artifacts from Linux systems; legal considerations; file identification and profiling initial analysis of a suspect file on a Linux system; and analysis of a suspect program.
This book will appeal to computer forensic investigators, analysts, and specialists.
- A compendium of on-the-job tasks and checklists
- Specific for Linux-based systems in which new malware is developed every day
- Authors are world-renowned leaders in investigating and analyzing malicious code

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Douglas FosterThe Enchanting Colors of the Southwest: Experience Nature's Local Masterpiece
Douglas FosterThe Enchanting Colors of the Southwest: Experience Nature's Local Masterpiece
 George BellThe Mysterious World of Atlantis: Unveiling the Secrets of the Antediluvian...
George BellThe Mysterious World of Atlantis: Unveiling the Secrets of the Antediluvian... Jared NelsonFollow ·5.8k
Jared NelsonFollow ·5.8k Alexander BlairFollow ·18.5k
Alexander BlairFollow ·18.5k Evan SimmonsFollow ·10.9k
Evan SimmonsFollow ·10.9k Ryūnosuke AkutagawaFollow ·7.4k
Ryūnosuke AkutagawaFollow ·7.4k Francis TurnerFollow ·17k
Francis TurnerFollow ·17k Denzel HayesFollow ·11.7k
Denzel HayesFollow ·11.7k Federico García LorcaFollow ·7.2k
Federico García LorcaFollow ·7.2k Easton PowellFollow ·7.2k
Easton PowellFollow ·7.2k