Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
The Ultimate Packet Guide To Core Network Protocols: Unlocking the Secrets!

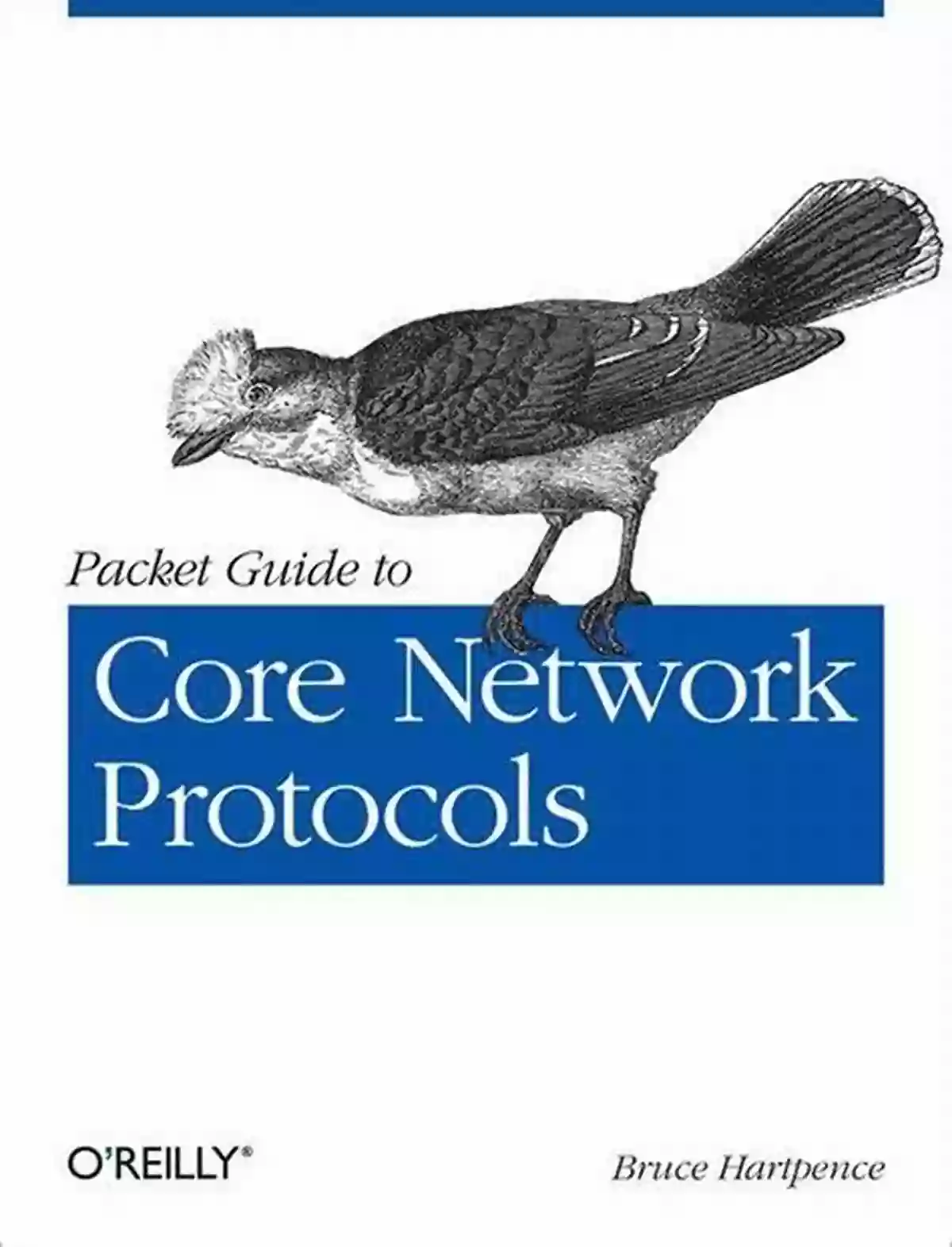
In today's interconnected world, network protocols play a crucial role in delivering data from one point to another. Understanding the core network protocols is essential for network administrators, engineers, and anyone who wants a deep dive into the inner workings of the internet. This comprehensive packet guide aims to demystify the fundamental protocols that power our digital communication networks.
What Are Network Protocols?
Network protocols are a set of rules or guidelines that govern the way data is transmitted, received, and processed over a network. They ensure that devices can communicate effectively and securely. Without network protocols, the internet as we know it would not exist.
4.2 out of 5
| Language | : | English |
| File size | : | 21299 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 266 pages |
Layered Communication Model
The OSI (Open Systems Interconnection) model is a conceptual framework that defines how different network protocols interact and communicate with each other. It consists of seven layers, each responsible for specific tasks in the transmission and reception of data.
Layer 1: Physical Layer
The physical layer is responsible for transmitting raw data over the physical medium, such as copper wires or fiber optic cables. It defines electrical and physical specifications for devices, such as Ethernet cables and wireless transceivers.
Layer 2: Data Link Layer
The data link layer is responsible for establishing and maintaining reliable connections between adjacent network nodes. It includes protocols such as Ethernet, PPP (Point-to-Point Protocol),and Wi-Fi.
Layer 3: Network Layer
The network layer handles the routing of data packets across multiple networks. The key protocol at this layer is the Internet Protocol (IP),which enables end-to-end communication between devices connected to different networks.
Layer 4: Transport Layer
The transport layer ensures the proper delivery of data between source and destination devices. Key protocols at this layer include TCP (Transmission Control Protocol) and UDP (User Datagram Protocol),which provide reliable and connectionless communication, respectively.
Layer 5: Session Layer
The session layer establishes, manages, and terminates sessions between devices. It enables synchronization and checkpointing of data during communication. Some common protocols at this layer include NetBIOS (Network Basic Input/Output System) and SSH (Secure Shell).
Layer 6: Presentation Layer
The presentation layer is responsible for data formatting and representation. It ensures that data is in a format that can be interpreted by the receiving device. Protocols at this layer include MIME (Multipurpose Internet Mail Extensions) and TLS (Transport Layer Security).
Layer 7: Application Layer
The application layer is the closest layer to the end user and includes protocols and services that directly interact with applications. Examples include HTTP (Hypertext Transfer Protocol),FTP (File Transfer Protocol),and DNS (Domain Name System).
Fundamental Network Protocols
Now that we have a basic understanding of the layered model, let's explore some of the core network protocols that operate at various layers:
Internet Protocol (IP)
The Internet Protocol (IP) is the foundation of the internet. It provides a unique address (IP address) to each device connected to a network and enables the routing of data packets from the source to the destination.
Transmission Control Protocol (TCP)
TCP is a reliable and connection-oriented protocol that ensures the successful delivery of data packets over a network. It guarantees the ordered delivery and error recovery, making it ideal for applications requiring high reliability.
User Datagram Protocol (UDP)
UDP is a connectionless and unreliable protocol that allows the quick transmission of data packets without any guarantee of delivery. It is commonly used for real-time applications such as video streaming and online gaming, where speed is prioritized over reliability.
Network protocols are the backbone of modern digital communication. Each protocol plays a vital role in ensuring the smooth flow of data across networks. By understanding how these core network protocols function, network administrators and engineers can optimize and troubleshoot their networks effectively. Whether you are a beginner or an experienced professional, this comprehensive packet guide equips you with the knowledge needed to unlock the secrets behind the core network protocols.
4.2 out of 5
| Language | : | English |
| File size | : | 21299 KB |
| Text-to-Speech | : | Enabled |
| Enhanced typesetting | : | Enabled |
| Print length | : | 266 pages |
Take an in-depth tour of core Internet protocols and learn how they work together to move data packets from one network to another. With this updated edition, you’ll dive into the aspects of each protocol, including operation basics and security risks, and learn the function of network hardware such as switches and routers. New chapters examine the transmission control protocol (TCP) and user datagram protocol in detail.
Ideal for beginning network engineers, each chapter in this book includes a set of review questions, as well as practical, hands-on lab exercises.
You’ll explore topics including:
- Basic network architecture: how protocols and functions fit together
- The structure and operation of the Ethernet protocol
- TCP/IP protocol fields, operations, and addressing used for networks
- The address resolution process in a typical IPv4 network
- Switches, access points, routers, and components that process packets
- TCP details, including packet content and client-server packet flow
- How the Internet Control Message Protocol provides error messages during network operations
- How network mask (subnetting) helps determine the network
- The operation, structure, and common uses of the user datagram protocol

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Greg FosterFargo And Moorhead Images Of America: Exploring the Past and Celebrating the...
Greg FosterFargo And Moorhead Images Of America: Exploring the Past and Celebrating the...
 Cole PowellThe Amazing Adventure of Hop the Little Frog and Dot the Ladybug: A Journey...
Cole PowellThe Amazing Adventure of Hop the Little Frog and Dot the Ladybug: A Journey...
 Jamie BlairFrom Gandhi's Porbandar to the Partitions: A Captivating Tale of Resilience -...
Jamie BlairFrom Gandhi's Porbandar to the Partitions: A Captivating Tale of Resilience -... Pete BlairFollow ·15.9k
Pete BlairFollow ·15.9k Amir SimmonsFollow ·13.1k
Amir SimmonsFollow ·13.1k Joseph ConradFollow ·18.3k
Joseph ConradFollow ·18.3k Evan SimmonsFollow ·10.9k
Evan SimmonsFollow ·10.9k Chase SimmonsFollow ·4.4k
Chase SimmonsFollow ·4.4k Jacob HayesFollow ·12k
Jacob HayesFollow ·12k Douglas AdamsFollow ·13.8k
Douglas AdamsFollow ·13.8k Virginia WoolfFollow ·5.3k
Virginia WoolfFollow ·5.3k