Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
Unveiling the Power of Obfuscation, Watermarking, and Tamperproofing for Ultimate Software Protection

In the ever-evolving digital landscape, protecting software against unauthorized access and intellectual property theft has become a paramount concern for developers and enterprises. With cyber threats looming large, it is imperative to adopt robust measures to safeguard proprietary code and ensure its integrity throughout its lifecycle. Enter the trio of obfuscation, watermarking, and tamperproofing techniques that can provide an impenetrable shield to your software assets, rendering them resilient against reverse engineering, piracy, and tampering attempts.
Understanding Obfuscation
Obfuscation is a technique used to make software code unreadable and unintelligible to external actors while preserving its functionality. By obfuscating code, developers can significantly enhance the security of their software, as it becomes arduous for hackers to understand the logic behind the implementation.
Obfuscation involves altering the software's code structure, renaming variables and functions, inserting meaningless code fragments, employing encryption algorithms, and more. This transformation disguises the original source code, making it difficult for attackers to analyze and comprehend its inner workings.
5 out of 5
| Language | : | English |
| File size | : | 10687 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 778 pages |
Exploring Watermarking Techniques
Watermarking is a novel technique employed to embed unique identification marks within software programs. These marks can be used to prove the ownership of the code, detect copyright infringements, and facilitate the tracking of illegal distributions.
By embedding a watermark within software, developers can trace the origin of unauthorized copies and identify the perpetrators involved in intellectual property theft. Watermarks can be designed to be invisible or easily recognizable, depending on the intended purpose.
Tamperproofing for Enhanced Protection
Tamperproofing, as the name suggests, aims to prevent any modifications or alterations to the software. It protects against tampering attempts, ensuring the integrity and authenticity of the code.
Tamperproofing techniques involve adding integrity-checking mechanisms, such as checksums and digital signatures, to the code. These mechanisms help identify any unauthorized changes to the software, alerting the system to potential security breaches.
The Power of Combined Forces
While each technique – obfuscation, watermarking, and tamperproofing – brings its own set of advantages, the real power lies in their combined deployment. When used in unison, these techniques create multiple layers of defense, reinforcing the security posture of the software.
Obfuscation makes the code incomprehensible to attackers, creating a deterrent for reverse engineering and hacking attempts. Watermarking adds traceability, enabling the identification of stolen code and facilitating legal actions. Tamperproofing offers protection against unauthorized modification, guaranteeing the code's originality and integrity.
In an era where software breaches have dire consequences, employing robust protection mechanisms is a necessity. Obfuscation, watermarking, and tamperproofing complement each other by providing multiple levels of defense against various cyber threats, ensuring that your software remains secure and impervious to unauthorized access, piracy, reverse engineering, and tampering attempts.
By leveraging the power of these techniques, developers and enterprises can safeguard their valuable software assets, protect their intellectual property, and maintain a competitive edge in the ever-advancing domain of software development.
5 out of 5
| Language | : | English |
| File size | : | 10687 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 778 pages |
“This book gives thorough, scholarly coverage of an area of growing importance in computer security and is a ‘must have’ for every researcher, student, and practicing professional in software protection.”
—Mikhail Atallah, Distinguished Professor of Computer Science at Purdue University
Theory, Techniques, and Tools for Fighting Software Piracy, Tampering, and Malicious Reverse Engineering
The last decade has seen significant progress in the development of techniques for resisting software piracy and tampering. These techniques are indispensable for software developers seeking to protect vital intellectual property. Surreptitious Software is the first authoritative, comprehensive resource for researchers, developers, and students who want to understand these approaches, the level of security they afford, and the performance penalty they incur.
Christian Collberg and Jasvir Nagra bring together techniques drawn from related areas of computer science, including cryptography, steganography, watermarking, software metrics, reverse engineering, and compiler optimization. Using extensive sample code, they show readers how to implement protection schemes ranging from code obfuscation and software fingerprinting to tamperproofing and birthmarking, and discuss the theoretical and practical limitations of these techniques.
Coverage includes
- Mastering techniques that both attackers and defenders use to analyze programs
- Using code obfuscation to make software harder to analyze and understand
- Fingerprinting software to identify its author and to trace software pirates
- Tamperproofing software using guards that detect and respond to illegal modifications of code and data
- Strengthening content protection through dynamic watermarking and dynamic obfuscation
- Detecting code theft via software similarity analysis and birthmarking algorithms
- Using hardware techniques to defend software and media against piracy and tampering
- Detecting software tampering in distributed system
- Understanding the theoretical limits of code obfuscation

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Aldous HuxleyThe Ultimate Windows Portable Command Guide: Master the MCTS 70-680, 70-685,...
Aldous HuxleyThe Ultimate Windows Portable Command Guide: Master the MCTS 70-680, 70-685,...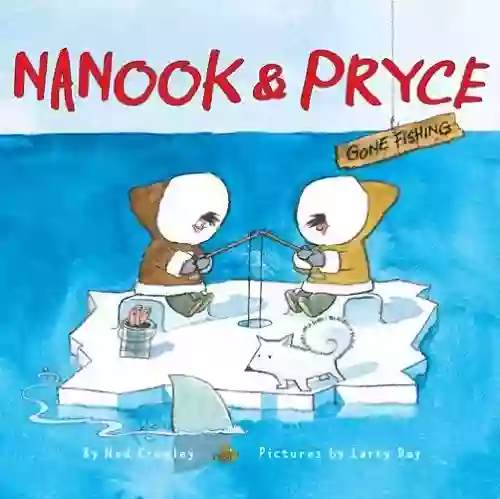
 William GoldingThe Incredible Journey of Nanook Pryce Gone Fishing: Join the Adventure with...
William GoldingThe Incredible Journey of Nanook Pryce Gone Fishing: Join the Adventure with...
 Noah BlairThe Epic Journey: History of Himalayan Mountaineering from the Age of Empire...
Noah BlairThe Epic Journey: History of Himalayan Mountaineering from the Age of Empire... Arthur MasonFollow ·13.7k
Arthur MasonFollow ·13.7k Jesus MitchellFollow ·11.5k
Jesus MitchellFollow ·11.5k Ethan MitchellFollow ·17.7k
Ethan MitchellFollow ·17.7k Henry HayesFollow ·4.9k
Henry HayesFollow ·4.9k Jedidiah HayesFollow ·16.1k
Jedidiah HayesFollow ·16.1k Ernest ClineFollow ·19.1k
Ernest ClineFollow ·19.1k Federico García LorcaFollow ·7.2k
Federico García LorcaFollow ·7.2k Logan CoxFollow ·16.1k
Logan CoxFollow ·16.1k