Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
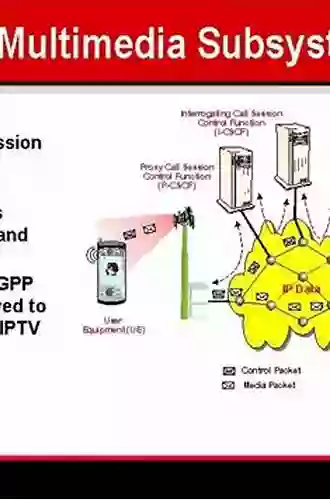
Amazing Session Control and Other Network Operations That Will Blow Your Mind!

Are you ready to dive into the fascinating world of session control and other network operations? From managing multiple users to ensuring smooth data transfer, network operations play a crucial role in keeping the digital world connected. In this article, we will unravel the secrets behind session control and explore other vital network operations that are essential for seamless communication. So, fasten your seatbelts and get ready to be blown away by the incredible capabilities of modern networking technology!
Understanding Session Control: The Backbone of Network Communication
Session control is the foundation on which reliable network communication is built. Imagine yourself as a user, trying to access a website or transfer data from your device. When you initiate communication, your device establishes a session with the destination server. This session acts as a virtual connection between your device and the server, allowing for smooth information exchange.
But how does session control ensure that your data reaches its destination without any hiccups? The answer lies in the underlying protocols and techniques used to maintain these sessions. Various protocols, such as TCP (Transmission Control Protocol) and UDP (User Datagram Protocol),govern how data packets are transmitted and received.
5 out of 5
| Language | : | English |
| File size | : | 3805 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 224 pages |
To maintain a reliable session, TCP utilizes a three-way handshake mechanism. This means that before any information is exchanged, a SYN (synchronize) packet is sent from the client to the server, followed by an ACK (acknowledge) packet from the server back to the client. Finally, another ACK packet is sent from the client to the server, confirming the establishment of a stable session. This process ensures that both ends are ready to exchange data and creates a reliable connection for further communication.
On the other hand, UDP offers a lightweight alternative to TCP. It does not require the establishment of a session and does not guarantee reliable packet delivery. However, UDP is extremely useful in scenarios where real-time communication is necessary, such as video streaming or online gaming. Despite its lack of reliability, UDP enables faster transmission speeds, making it a popular choice for time-sensitive applications.
Network Operations: The Building Blocks of a Connected World
Beyond session control, several other network operations contribute to the efficient functioning of today's interconnected systems. Let's take a closer look at some of the key operations that are vital for network connectivity:
1. Routing
Routing is essential for directing data packets between different networks. When a packet is sent from one device to another, it goes through various routers along the way. These routers analyze the packet's destination address and determine the best path for its delivery. By dynamically building routing tables, routers ensure that data reaches its intended destination efficiently.
2. Switching
Switching plays a significant role in connecting devices within a local network. Switches are responsible for directing data packets between different ports, allowing devices to communicate with each other. They examine the destination MAC (Media Access Control) address of packets and forward them accordingly, optimizing network performance and reducing congestion.
3. VLANs (Virtual Local Area Networks)
VLANs are a powerful tool for creating logical network segments within a physical infrastructure. By using VLANs, network administrators can separate devices into different virtual networks, enhancing security and network management. VLANs enable efficient broadcast control and offer scalability by allowing for logical segregation without the need for physical infrastructure changes.
4. Quality of Service (QoS)
In today's data-driven world, maintaining a high level of service quality is of utmost importance. Quality of Service (QoS) is a network operation that allows network administrators to prioritize specific types of traffic, ensuring consistent performance for critical applications. By assigning different levels of priority to data packets based on their type or source, QoS helps prevent network congestion and guarantees reliable performance.
From session control to routing and switching, network operations play a vital role in keeping our digital world connected. Understanding these operations allows us to appreciate the complexity and incredible capabilities that make modern networking possible.
So next time you establish a session or experience smooth data transfer, remember the intricate protocols and mechanisms that lay the groundwork for seamless communication. The world of network operations is truly fascinating, and we have only scratched the surface! Explore further, and you'll discover a plethora of cutting-edge technologies that shape our interconnected lives.
5 out of 5
| Language | : | English |
| File size | : | 3805 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 224 pages |
Build and maintain a converged multimedia network environment
Seamlessly merge the Internet with cellular and wireless networks using next-generation IMS technology and the comprehensive information contained in this authoritative resource. The IP Multimedia Subsystem: Session Control and Other Network Operations details the steps necessary to deliver Web-based content, VoIP, streaming multimedia, conference calls, and text messages across one integrated network. Learn how to transition to IMS architecture, communicate with legacy networks, control sessions using SIP, and connect subscribers to network services. In-depth coverage of the latest IMS security, business intelligence, customer care, and billing procedures is also included.
- Migrate legacy networks to IMS-based technology
- Use the Proxy, Interrogating, and Serving Call Session Control Functions
- Interface with TDM-based, wireless, wireline, and VoIP networks
- Handle private and public user identities, domain names, and URLs
- Establish SIP sessions and connect subscribers to network services
- Deploy reliable network, access, and user-level security
- Prevent eavesdropping, DoS, message tampering, and amplification exploits
- Track services rendered and charge subscribers using DIAMETER and CDRs

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Lee SimmonsThe Comprehensive Handbook of Catchment Management: Discover the Insights of...
Lee SimmonsThe Comprehensive Handbook of Catchment Management: Discover the Insights of...
 Darren BlairUnleashing the Magic Within: The Enchanting World of Wiccan Chants - Revised...
Darren BlairUnleashing the Magic Within: The Enchanting World of Wiccan Chants - Revised... Thomas PynchonFollow ·11.3k
Thomas PynchonFollow ·11.3k Ernest ClineFollow ·19.1k
Ernest ClineFollow ·19.1k Lord ByronFollow ·5.1k
Lord ByronFollow ·5.1k Theodore MitchellFollow ·12.8k
Theodore MitchellFollow ·12.8k Zadie SmithFollow ·7.3k
Zadie SmithFollow ·7.3k Herman MitchellFollow ·5.7k
Herman MitchellFollow ·5.7k Fernando BellFollow ·15.6k
Fernando BellFollow ·15.6k Tom ClancyFollow ·5.4k
Tom ClancyFollow ·5.4k