Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
5 Insane Hacks You Didn't Know Were Possible: Facebook Hack, Linux Hack, Wifi Hack

Technology has revolutionized our lives in numerous ways, but it has also opened the doors to hacking and cyber threats. In this article, we explore some mind-blowing hacks that you probably never knew were possible: hacking Facebook, Linux, and wifi networks. Brace yourself for an incredible journey into the world of digital intrusions!
1. Facebook Hack: Unmasking the Secrets
Facebook, being the world's largest social media platform, is a prime target for hackers. You may have heard stories about someone's Facebook account getting hacked, but have you ever wondered how it's done?
The process involves exploiting vulnerabilities in Facebook's security mechanisms, such as weak passwords, unsecured Wi-Fi networks, or even manipulating the user's trust. Once hackers gain access to an account, they can wreak havoc, stealing personal information, spreading malicious content, and even conducting social engineering attacks.
4.5 out of 5
| Language | : | English |
| File size | : | 53 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 8 pages |
| Lending | : | Enabled |
To protect your Facebook account, it's essential to have a strong password, enable two-factor authentication, and be wary of suspicious links or messages.
2. Linux Hack: Unleashing its Power
Linux, an open-source operating system, offers unparalleled flexibility and security. However, even this robust system can be hacked if certain security measures are not in place.
Linux-based systems are commonly targeted due to their prevalence in various industries, including servers and IoT devices. Hackers aim to exploit vulnerabilities in outdated software, weak passwords, or even insider threats to gain unauthorized access.
To protect your Linux system, it is crucial to keep your software up to date, apply patches regularly, and implement proper access controls. Additionally, monitoring network traffic and configuring firewalls can help detect and prevent potential attacks.
3. Wifi Hack: Cracking the Code
Wi-Fi networks, present in almost every home and public place, can be a goldmine for hackers seeking access to sensitive data or even launching larger-scale attacks.
Wifi hacking techniques range from simple password cracking to more sophisticated methods, such as exploiting weak encryption algorithms or compromising router security settings.
To secure your wifi network, experts recommend using strong encryption protocols, changing default passwords, hiding your network's SSID, and regularly updating your router's firmware.
4. Protecting Yourself from Unwanted Intrusions
Now that we've delved into these mind-blowing hacks, it's essential to understand how to protect yourself from becoming a victim.
Firstly, ensure you have strong, unique passwords for all your online accounts, including social media platforms and email services. Enabling two-factor authentication whenever possible adds an extra layer of security.
Furthermore, keep your devices and software up to date, as these updates often contain security patches to address vulnerabilities. Regularly backup your data to avoid the risk of losing everything in the event of a successful hack.
5. The Bright Side of Hacking: Ethical Hacking
While hacking is often associated with negative connotations, there's a positive side known as ethical hacking. Ethical hackers, also known as white hat hackers, use their skills to identify vulnerabilities in systems and help organizations strengthen their security.
Ethical hacking involves obtaining explicit permission from the target organization, conducting tests, analyzing weaknesses, and providing recommendations to enhance their security posture. These experts play a crucial role in defending against malicious hackers and safeguarding sensitive information.
The world of hacking is vast, and it's vital to remain vigilant against potential intrusions. Understanding these hacks and taking preventative measures helps protect your digital presence.
Remember to use strong passwords, implement two-factor authentication, keep your software updated, and regularly backup your data. By taking these steps, you can minimize the risk of falling victim to cyber threats and take control of your digital security.
4.5 out of 5
| Language | : | English |
| File size | : | 53 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 8 pages |
| Lending | : | Enabled |
About This Book:
You are so vulnerable In any Open Network,
When a network device is connected to any network that is not safe and secure In This Book
1.How to wifi hack
2.How facebook hack
3.How to linux system hack
All details discuss We are not secure in
the network so feel think connect and click any lin

 Richard Simmons
Richard SimmonsThe Secrets of Chaplaincy: Unveiling the Pastoral...
Chaplaincy is a field that encompasses deep...

 Manuel Butler
Manuel ButlerAnimales Wordbooks: Libros de Palabras para los Amantes...
Si eres un amante de los animales como yo,...

 Rod Ward
Rod WardLet's Learn Russian: Unlocking the Mysteries of the...
Are you ready to embark...

 Rod Ward
Rod WardThe Incredible Adventures of Tap It Tad: Collins Big Cat...
Welcome to the enchanting world of...

 Eugene Powell
Eugene PowellSchoolla Escuela Wordbookslibros De Palabras - Unlocking...
Growing up, one of the most significant...

 José Martí
José Martí15 Exciting Fun Facts About Canada for Curious Kids
Canada, the second-largest...

 Ken Simmons
Ken SimmonsWhat Did He Say? Unraveling the Mystery Behind His Words
Have you ever found yourself struggling to...

 Carlos Fuentes
Carlos FuentesA Delicious Journey through Foodla Comida Wordbookslibros...
Welcome to the world of Foodla Comida...

 Matt Reed
Matt ReedThe Many Colors of Harpreet Singh: Embracing...
In a world that often...

 Chandler Ward
Chandler WardWelcome To Spain Welcome To The World 1259
Welcome to Spain, a country that captivates...

 Garrett Powell
Garrett PowellAmazing Recipes for Appetizers, Canapes, and Toast: The...
When it comes to entertaining guests or...

 Emilio Cox
Emilio CoxDays And Times Wordbooks: The Ultimate Guide to Mastering...
In the realm of language learning,...
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Octavio PazMeet the adorable teacup pigs of Pennywell Farm: A farm paradise experience...
Octavio PazMeet the adorable teacup pigs of Pennywell Farm: A farm paradise experience...
 Guillermo BlairThe Ultimate Guide to the Glad To Be Dad Culture Connections: Unlocking...
Guillermo BlairThe Ultimate Guide to the Glad To Be Dad Culture Connections: Unlocking...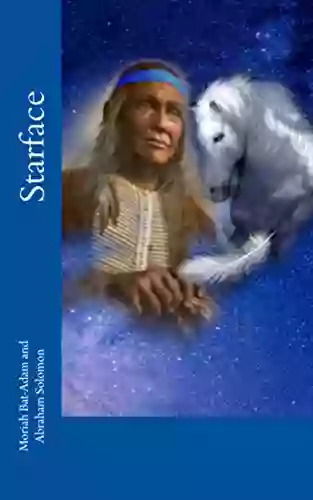
 Arthur C. ClarkeStarface Moriah Bat Adam - The Sensation Taking the Music Industry by Storm
Arthur C. ClarkeStarface Moriah Bat Adam - The Sensation Taking the Music Industry by Storm Charles DickensFollow ·18.6k
Charles DickensFollow ·18.6k Francisco CoxFollow ·8.7k
Francisco CoxFollow ·8.7k Dylan MitchellFollow ·11.2k
Dylan MitchellFollow ·11.2k Jacob FosterFollow ·17.8k
Jacob FosterFollow ·17.8k Brandon CoxFollow ·17.7k
Brandon CoxFollow ·17.7k Theodore MitchellFollow ·12.8k
Theodore MitchellFollow ·12.8k Roy BellFollow ·7.4k
Roy BellFollow ·7.4k Chinua AchebeFollow ·12.2k
Chinua AchebeFollow ·12.2k